Views: 1972

By default, CentOS 7 shipped with OpenSSL 1.0.2 and only TLSv 1.2 supported and needed to upgrade to OpenSSL 1.1.1 to enable TLSv 1.3 on Nginx server. Since CentOS 8 shifted their focus to becoming CentOS stream and not production ready, so I decided to continue working with CentOS 7 and waiting for the new RHEL fork like CentOS.
In this article, we will install the latest stable OpenSSL version 1.1.1i, before we start to configure and install, we need to install the development tools and some dependencies below:
$ sudo yum -y install "Development Tools" perl-core zlib-devel
To install openssl from source, we need to download the source file from openssl.org:
$wget https://www.openssl.org/source/openssl-1.1.1i.tar.gz
Extract the file and start configure and installing OpenSSL from source:
$ tar -zxf openssl-1.1.1i.tar.gz
$ cd openssl-1.1.1i
$ ./config shared no-idea no-md2 no-mdc2 no-rc5 no-rc4 \
--prefix=/usr/local/openssl
$ make -j$nproc
$ sudo make install
After the OpenSSL installation from source completed, we can verify the OpenSSL version by using command below:
$/usr/local/openssl/bin/openssl version
OpenSSL 1.1.1i 8 Dec 2020 (Library: OpenSSL 1.1.1g FIPS 21 Apr 2020)
Next, we will install nginx from source and enable TLSv 1.3 on nginx, we will use version 1.19.6:
$ wget http://nginx.org/download/nginx-1.19.6.tar.gz
$ tar -zxf nginx-1.19.6.tar.gz
$ cd nginx-1.19.6
$ ./configure --prefix=/usr/local/nginx --with-threads \
--with-file-aio --with-http_ssl_module --with-http_v2_module \
--with-http_realip_module --with-http_addition_module \
--with-http_xslt_module --with-http_gunzip_module \
--with-http_gzip_static_module --with-http_random_index_module \
--with-http_secure_link_module --with-pcre --with-debug \
--with-http_stub_status_module --with-compat --with-http_geoip_module \
--with-http_sub_module --with-http_flv_module --with-http_mp4_module \
--with-http_gunzip_module --with-http_gzip_static_module \
--with-http_random_index_module --with-http_slice_module \
--with-cc-opt="-I/usr/local/openssl/include" \
--with-ld-opt="-L/usr/local/openssl/lib"
$ make -j$nproc
$ sudo make install
After the nginx installation completed, then check the nginx version use command below:
$/usr/local/nginx/sbin/nginx -V
And please see image below:

To enable TLSv 1.3 on nginx we need to change the virtual host setting on nginx server block like below:
ssl_protocols TLSv1.2 TLSv1.3;
And here is the complete of virtual host in nginx with TLSv 1.3 enabled:
server {
listen 443 ssl http2 ;
server_name pnyet.web.id www.pnyet.web.id;
root /home/pnyet/public_html;
index index.php index.html;
ssl_certificate /etc/letsencrypt/live/pnyet.web.id/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/pnyet.web.id/privkey.pem;
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem;
ssl_protocols TLSv1.2 TLSv1.3; ssl_prefer_server_ciphers on; ssl_ciphers "ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!3DES:!MD5:!PSK";
ssl_session_cache shared:SSL:10m;
ssl_session_timeout 5m;
ssl_stapling on;
ssl_stapling_verify on;
resolver 127.0.0.1 1.1.1.1 8.8.8.8 4.2.2.1 8.8.4.4 4.2.2.2 valid=300s;
resolver_timeout 5s;
location = /favicon.ico { log_not_found off; }
access_log logs/pnyet.web.id_access.log basic;
error_log logs/pnyet.web.id_error.log notice;
location ~ \.php$ {
try_files $uri =404;
fastcgi_pass 127.0.0.1:9000;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
include fastcgi_params;
}
location ~ /.well-known {
root /home/pnyet/.well-known; allow all; }
location / {
client_max_body_size 2000m;
client_body_buffer_size 512k;
try_files $uri $uri/ /index.php?$query_string; }
}
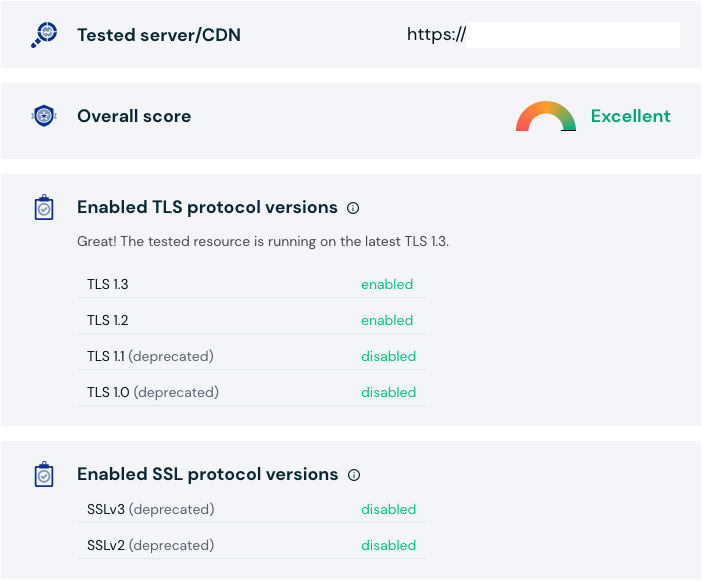
#End of nginx virtualhost configuration for pnyet.web.idThere are several websites that provide TLS version checking and we can verify the TLS 1.3 in nginx wokring, I used sslabs and cdn77 to test the TLS 1.3 are enabled on nginx.. Please see below:
All done, and if you have any problem or questions installing or enabling TLS 1.3 on nginx CentOS 7 please leave a comment below. I’ll do my best reply your comment.